The MPC Revolution: Why Multi-Sig is No Longer the Institutional Standard in 2026
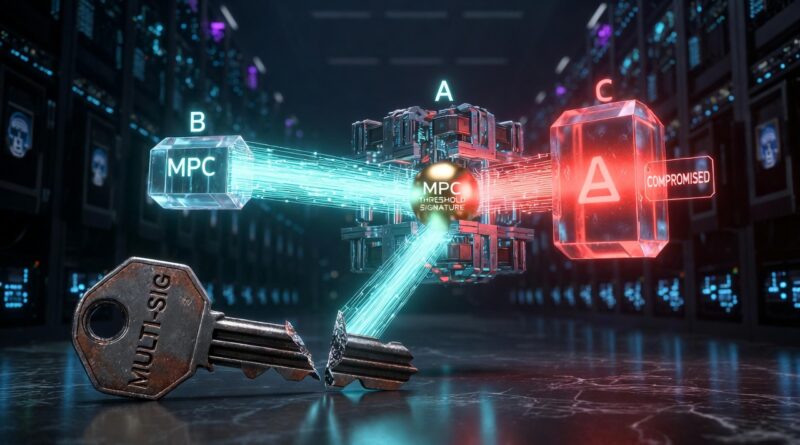
The “gold standard” of digital asset security is undergoing a silent, mathematical coup. For the better part of a decade, the crypto industry relied on Multi-Signature (Multi-Sig) wallets as the ultimate barrier against theft. The logic was simple: if one key is compromised, the assets remain safe because the attacker needs two or three. However, as we cross into mid-2026, this “on-chain” transparency has transformed from a feature into a tactical liability for institutional capital.
In the current landscape, sophisticated attackers are no longer just hunting for private keys; they are mapping out governance structures. Traditional Multi-Sig setups like those popularized by Gnosis Safe expose the “who” and the “how” of a fund’s security directly on the public ledger. In an era where AI-driven forensics can correlate signing patterns with social engineering targets, being transparent about your security architecture is equivalent to handing over the blueprints of your vault.
My Critical Take: The “Transparency” Trap
In my opinion, the financial industry’s obsession with “on-chain transparency” has backfired. We were sold the narrative that seeing every signature on the ledger was a triumph of trust. But for an institutional treasurer in 2026, this is a glaring security hole.
Multi-Sig is rigid. It is tethered to specific smart contract logic that varies from one blockchain to another, creating “silos” of security that are expensive to maintain and slow to execute. More importantly, it forces a trade-off between speed and safety that no serious wealth manager should accept. The transition to MPC (Multi-Party Computation) isn’t just a technical upgrade; it is a move toward operational privacy. By taking the signature process off-chain, we are finally separating “proof of intent” from “exposure of architecture.”
Analyst’s Warning: If your security strategy relies on the attacker not knowing who your signers are, but your blockchain records tell the whole story, you aren’t being decentralized you are being predictable.
The Architecture of Invisible Trust: What is MPC?
Multi-Party Computation (MPC) represents a fundamental shift in how we define a “private key.” In a traditional wallet or even a cold storage device like a Ledger or Trezor the key exists as a single, identifiable digital object. Even in a Multi-Sig, you are simply managing multiple “single objects.”
MPC changes the math. Through a process known as Threshold Cryptography, the private key never actually exists as a whole. Instead, it uses a protocol where multiple parties each hold a “shard” of the key.
Table 1: 2026 Institutional Custody Benchmark
| Feature | Multi-Sig (Traditional) | MPC (Threshold Signature) | HSM (Hardware Security) |
| Execution Layer | On-Chain (Smart Contract) | Off-Chain (Math) | Hardware Enclave |
| Gas Efficiency | Low (Multiple Sigs = $$$) | Highest (Single Sig Cost) | Medium |
| Chain Support | Chain-Specific (EVM only, etc.) | Universal (BTC, ETH, SOL) | High |
| Privacy | Public (Signers are visible) | Private (Signers hidden) | Private |
| Key Recovery | Complex (On-chain consensus) | Dynamic (Resharding) | Provider Dependent |
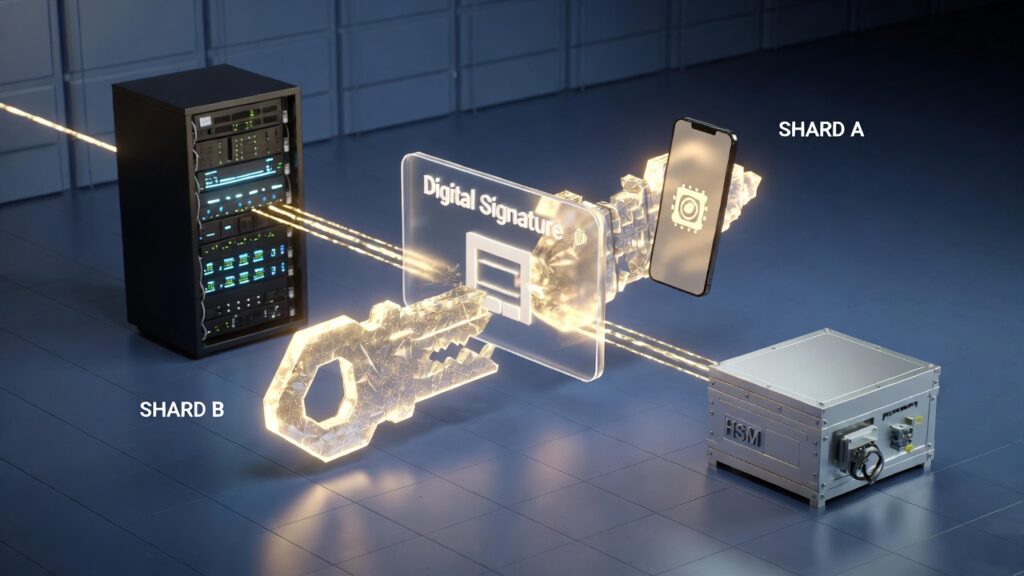
2026 MPC Architecture in action. Key shards are distributed across isolated environments (Cloud Server, Mobile, and HSM) to generate a threshold signature without ever reconstructing the full private key on a single device.
Why the “Sharded” Approach Wins in 2026
By analyzing the current threat vectors, it’s clear why institutions like Fireblocks and Anchorage Digital have pivoted almost exclusively to MPC-based architectures.
- Key Sharding: The key is generated in shards across independent nodes. No single person or server ever sees the full key.
- Zero-Knowledge Interaction: When a transaction requires a signature, the shards interact mathematically to produce a valid signature without ever “reconstructing” the key. It’s like a puzzle that solves itself without the pieces ever touching.
- Agnosticism: Because the signature happens off-chain, an MPC wallet works identically on Bitcoin, Ethereum, or the latest Layer-3, without needing to deploy new smart contracts for every chain.
This layer of abstraction is what allows for 1099-DA compliance and institutional-grade auditing without exposing sensitive internal movements to the public eye.
The “Policy Engine”: The Brain Behind the Mathematical Vault
If the MPC shards are the “locks,” the Policy Engine is the architect that decides when and why those locks should open. In my experience, the biggest mistake institutional newcomers make is focusing solely on the “key” and ignoring the governance layer.
A private key is just a tool; the policy engine is the set of rules that governs its use. By 2026, leading platforms like Fireblocks and Anchorage Digital have moved beyond simple “who signs” logic. Their engines now analyze contextual data in real-time before even triggering an MPC computation:
- Geofencing & IP Whitelisting: Is the signer in an approved jurisdiction or using a compromised VPN?
- Velocity Limits: Has this sub-wallet exceeded its $10M daily limit?
- Whitelisted Destinations: Is the funds’ destination a verified institutional OTC desk or a newly created “mixer” address?
Analyst’s Note: A robust policy engine must be independent of the signing shards. If an attacker compromises a signer’s device, the policy engine acts as a secondary, automated “veto” power that blocks the transaction based on behavioral anomalies.
MPC vs. The “Invisible” Compliance: Navigating the 1099-DA Era
As we move deeper into 2026, the regulatory landscape specifically the 1099-DA (Digital Asset) reporting requirements has made life difficult for traditional DeFi users. This is where MPC provides a massive competitive advantage.
Because MPC signatures happen off-chain, institutions can maintain internal privacy while still being externally compliant. They can provide regulators with “View Keys” or audit logs that prove a transaction was authorized by three specific officers, without ever revealing those officers’ public wallet addresses to the entire internet.
Table 2: Compliance and Operational Speed (2026 Benchmark)
| Operational Metric | Multi-Sig (On-Chain) | MPC (Off-Chain) |
| Audit Trail | Public & Permanent | Private & Auditable (Selective) |
| 1099-DA Reporting | Manual/Reactive | Automated/Proactive |
| Transaction Latency | High (Block confirmation) | Sub-second (Internal) |
| Signature Flexibility | Static (Hard to change) | Dynamic (Instant Resharding) |
My Critical Take: The “Vendor Lock-In” Dilemma
Let’s be brutally honest: MPC is not a perfect “silver bullet.” While it solves the transparency and gas problems of Multi-Sig, it introduces a new risk that many analysts are afraid to mention: Vendor Dependency.
If you use a specialized MPC provider and their servers go offline, or the company faces a sudden regulatory shutdown, your “shards” might become useless pieces of a puzzle you cannot complete. Unlike a Trezor or Ledger, where you can simply input your seed phrase into another device, MPC shards are often proprietary.
In my opinion, any institutional setup that doesn’t have a disaster recovery shard stored in a physical, air-gapped location (offline and independent of the provider) is just trading one type of risk for another. Convenience should never be a suicide pact with your service provider.
Bridging the Gap: MPC for the Retail Investor
Is this technology only for the “whales” and the hedge funds? Not anymore. In 2026, we are seeing the rise of “Cyborg Wallets” for retail users. Platforms like Zengo and Coinbase’s MPC-integrated wallets allow regular investors to enjoy “seedless” security.
- No Seed Phrase to Lose: You don’t have a 24-word phrase that can be stolen.
- 3D Liveness Check: The “shard” on your phone is only activated after a biometric scan that detects blood flow and micro-expressions (the defense against the Deepfakes we analyzed previously).
- Cloud Recovery: If you lose your phone, you can recover your shard through a multi-factor authentication process involving your email, a face scan, and a trusted third-party backup.
The Quantum Threat: Is MPC Future-Proof?
As we look toward the late 2020s, a new shadow looms over digital asset security: Quantum Computing. Critics often argue that while Multi-Sig is slow, its on-chain nature allows for easier hard-forks to quantum-resistant algorithms.
In my opinion, this is a flawed argument. MPC is not a static technology; it is a mathematical protocol. By 2026, we are already seeing the integration of Post-Quantum Cryptography (PQC) within MPC nodes. Because the signing happens off-chain, upgrading an MPC wallet to a quantum-resistant shard system is actually simpler than migrating millions of legacy on-chain addresses. MPC is not just the standard for today’s institutional capital; it is the bridge to the post-quantum era.
My Final Take: Privacy is the Ultimate Security Layer
The transition from Multi-Sig to MPC reflects a deeper shift in the 2026 market: the realization that visibility is a vulnerability. We have spent a decade celebrating the transparency of the blockchain, only to realize that for an institution, transparency is a target on its back.
Security in 2026 is no longer about having the biggest “lock.” It is about making the vault invisible. By decoupling the signature from the blockchain’s public view, MPC allows for a level of operational stealth that was previously impossible. If you are still relying on legacy on-chain multisigs, you are essentially defending a glass house with a wooden door.
2026 Institutional Audit Checklist (Summary)
Before committing capital to any custody solution this year, ensure it meets these three “Hard” requirements:
- Dynamic Resharding: The ability to rotate key shards without a blockchain transaction.
- Hardware-Backed Nodes: Shards must reside in TEEs (Trusted Execution Environments) or HSMs, never in plain software.
- Independent Policy Layer: A governance engine that can block a valid signature if it violates pre-set behavioral risk parameters.
Closing Thoughts
The “Cyborg Mindset” we discussed in my Strategy Manifesto requires us to be as analytical about our tools as we are about our trades. Digital asset custody has evolved from a technical necessity into a strategic weapon. In 2026, your choice of custody architecture whether it’s an air-gapped Tangem or Ledger for personal use or an MPC-led institutional stack will be the single most important factor in your long-term survival.
The era of “set and forget” security is dead. In the 2026 market, the only constant is the evolution of the threat. Verification is a daily discipline, and math is your only true ally.