Can AI Crack Your VPN? Why You Need Quantum-Resistant Encryption in 2026
The cybersecurity landscape has shifted from “computational difficulty” to “algorithmic intelligence.” For decades, VPN providers relied on the assumption that breaking AES-256 encryption would take millions of years. While that mathematical truth remains technically intact, Artificial Intelligence has found a way to bypass the front door entirely.
In 2026, the question is no longer whether AI can “crack” a code through brute force. The real threat lies in how machine learning models identify misconfigurations, traffic patterns, and metadata leaks that human auditors consistently miss. If you are still relying on a standard VPN protocol from two years ago, your digital perimeter is likely transparent to modern adversarial AI.
1. The Death of Anonymity through Traffic Correlation
Most users believe that as long as their data is “encrypted,” their activity is private. This is a dangerous misconception in the age of AI. Modern neural networks can now perform Traffic Correlation Attacks with over 98% accuracy.
By analyzing the timing, size, and frequency of data packets leaving your device, an AI can identify exactly what you are doing (streaming, browsing, or transacting) without ever breaking the encryption tunnel. This effectively invalidates the “no-logs” promise of many commercial VPNs. If the AI knows the “shape” of your data, it doesn’t need the key to the box to know what is inside.
2. AI-Optimized Side Channel Attacks
AI has dramatically reduced the margin of safety around cryptographic implementations. Instead of attacking the math, AI-driven tools now target the Side Channels:
- Timing Analysis: AI models can detect micro-fluctuations in server response times to guess portions of an encryption key.
- Predictable Entropy: Many VPN servers use weak random number generators. AI can predict these “random” sequences, making the “unbreakable” key remarkably easy to replicate.
This shift mirrors the institutional movement we analyzed in our report on Goldman Sachs’ $2.3B Crypto Roadmap, where the focus is no longer on speculative “noise” but on owning the underlying security infrastructure of the financial rails.
3. The VPN Marketing Trap: AES-256 is Not Enough
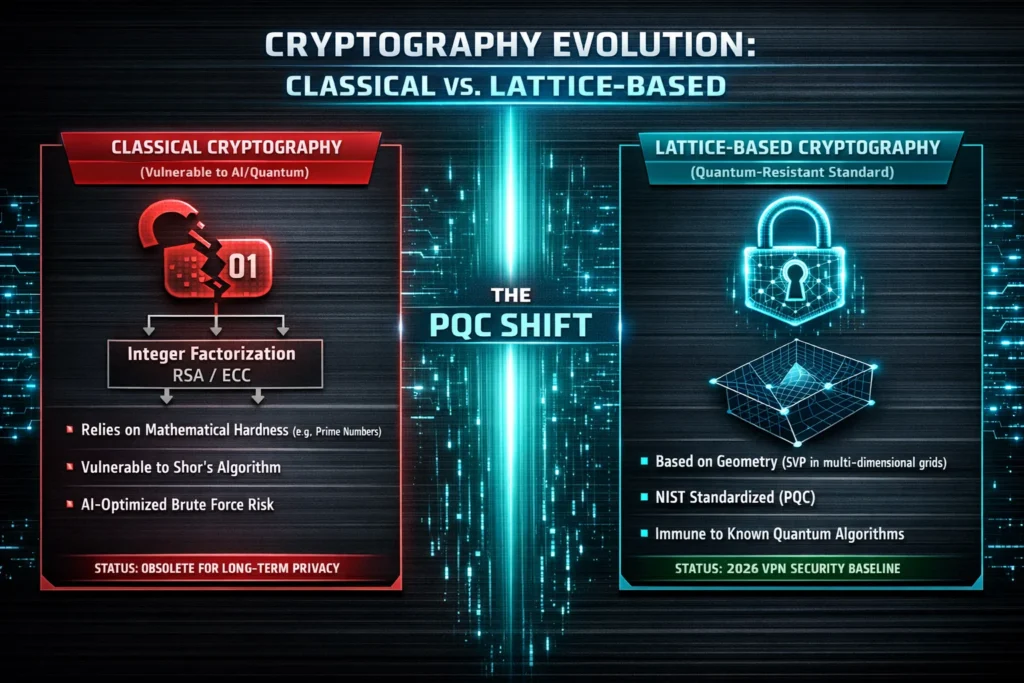
In 2026, many VPN providers still use “AES-256” as their primary marketing slogan. While AES-256 is robust, it is the Handshake Protocol (RSA or Elliptic Curve) that is the weak link.
Most VPNs use RSA-2048 or ECC for the initial connection. These are the specific protocols that are most vulnerable to the rise of specialized AI-cracking algorithms and early-stage quantum hardware. As an analyst, I must be direct: a VPN that does not openly discuss its transition to Post-Quantum Cryptography (PQC) is selling you a false sense of security.
Comparison: Traditional VPN vs. AI-Era Security (2026)
| Feature | Standard VPN (2024 Legacy) | Quantum-Resistant VPN (2026 Standard) |
| Encryption | AES-256 / RSA | AES-256-GCM / ML-KEM (Lattice-based) |
| Traffic Masking | Basic Obfuscation | AI-Resistant Packet Padding |
| Key Exchange | Elliptic Curve (ECDH) | Post-Quantum Hybrid Handshake |
| Threat Profile | Brute Force Protection | Correlation & Quantum Protection |
4. The Quantum Shadow: “Harvest Now, Decrypt Later”
The most sophisticated threat in 2026 isn’t a hacker trying to break your VPN today. It is the state-sponsored actor capturing your encrypted traffic to store it. This strategy, known as “Harvest Now, Decrypt Later” (HNDL), assumes that within the next few years, quantum-capable systems will be powerful enough to break current RSA and Elliptic Curve (ECC) handshakes retroactively.
If you are using a legacy VPN to handle sensitive financial data or private communications, that data is already at risk. Once a stable quantum computer running Shor’s Algorithm is deployed at scale, every “secure” tunnel from the last decade could be unmasked. In 2026, privacy is no longer just about the present; it is a battle for the future of your past data.
5. Post-Quantum Cryptography (PQC) is the New Standard
To counter the quantum threat, the industry has moved toward Lattice-based Cryptography. In late 2025, the transition to ML-KEM (formerly Kyber) and ML-DSA (Dilithium) became the baseline for high-security VPNs.
These algorithms are based on mathematical problems—specifically “Shortest Vector Problems” in multi-dimensional lattices that even quantum computers struggle to solve efficiently. If your VPN provider hasn’t updated its protocol stack to include a Quantum-Hybrid Handshake, they are essentially leaving the back door unlocked for the next decade of decryption technology.
6. Critical Verdict: Encryption is Not a Silver Bullet
As an analyst, I must be brutally honest: no VPN can protect you if your endpoint security is compromised. AI doesn’t need to break your VPN tunnel if it can find a vulnerability in your device’s operating system or guess your password through behavioral analysis.
This is why, in 2026, we see a massive shift toward Hardware-First Security. Whether you are protecting your browsing history or your life savings, the “digital air-gap” is the only true defense. As we explored in our Tangem Wallet Review: 2026 Security Analysis, moving your most sensitive digital keys to a dedicated, offline hardware element is the only way to remain immune to the AI-driven “brute-forcing” of the software world.
7. Choosing a VPN in the AI Era: The Checklist
Before renewing your subscription in 2026, verify these three technical requirements:
- Post-Quantum Hybrid Support: Does the provider use NIST-standardized PQC algorithms?
- AI-Resistant Obfuscation: Does the VPN use dynamic packet padding to prevent traffic correlation attacks?
- Infrastructure Ownership: Does the provider own their hardware, or are they renting “virtual” space from the same cloud giants we discussed in our Akash Network (AKT) Deep Dive ?
Comparison: The Cost of Privacy in 2026
| VPN Category | Security Level | Best Use Case | Risk Factor |
| Legacy VPN | Low (Vulnerable) | General Streaming | High (HNDL Risk) |
| Quantum-Ready | High (Standard) | Remote Work / Finance | Medium (Software Bugs) |
| Air-Gapped / PQC | Maximum (Elite) | Crypto Custody / High Risk | Low (Hardware-Bound) |
Final Thoughts: Adapt or Be Exposed
The era of “set it and forget it” privacy is over. AI and quantum computing have turned cybersecurity into an active arms race. In 2026, a VPN is merely one tool in a much larger survival kit. To stay truly private, you must treat your data like your capital: diversify your defenses, use hardware for your most critical assets, and never trust a “marketing buzzword” over a verified cryptographic audit.
The future of your privacy depends on your willingness to adapt before the threats fully arrive. If you are still using 2024 technology to protect 2026 data, you are already exposed.